The AI Agent For Product Security

Supercharge your engineering
Cut manual security reviews and 'black box' compliance audits
Periphery Insights integrates directly into your build process to extract live device evidence, eliminate hardcoded secrets, and map configuration components to global regulations.
It’s the fastest way to get from "code complete" to "audit ready" without the AppSec noise.
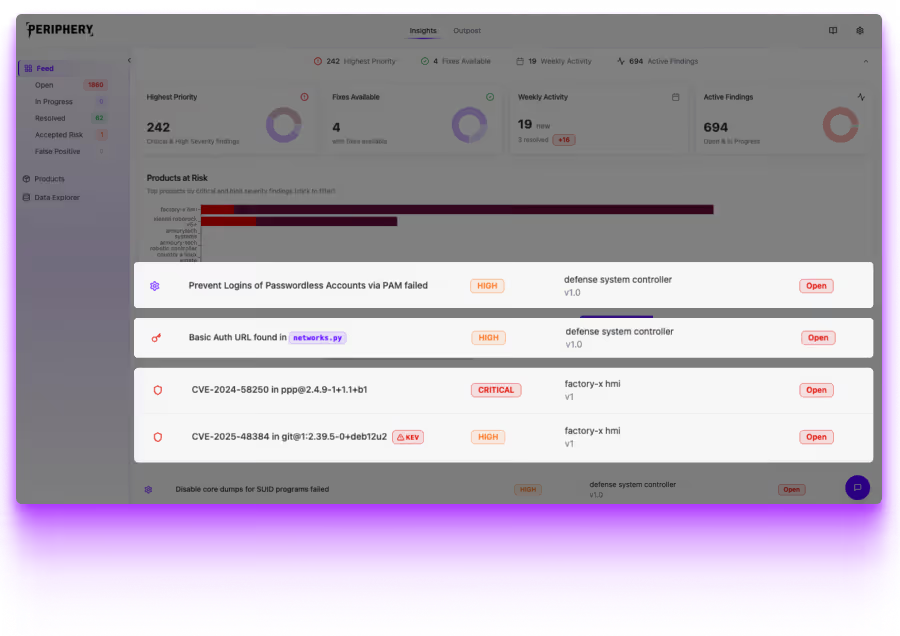
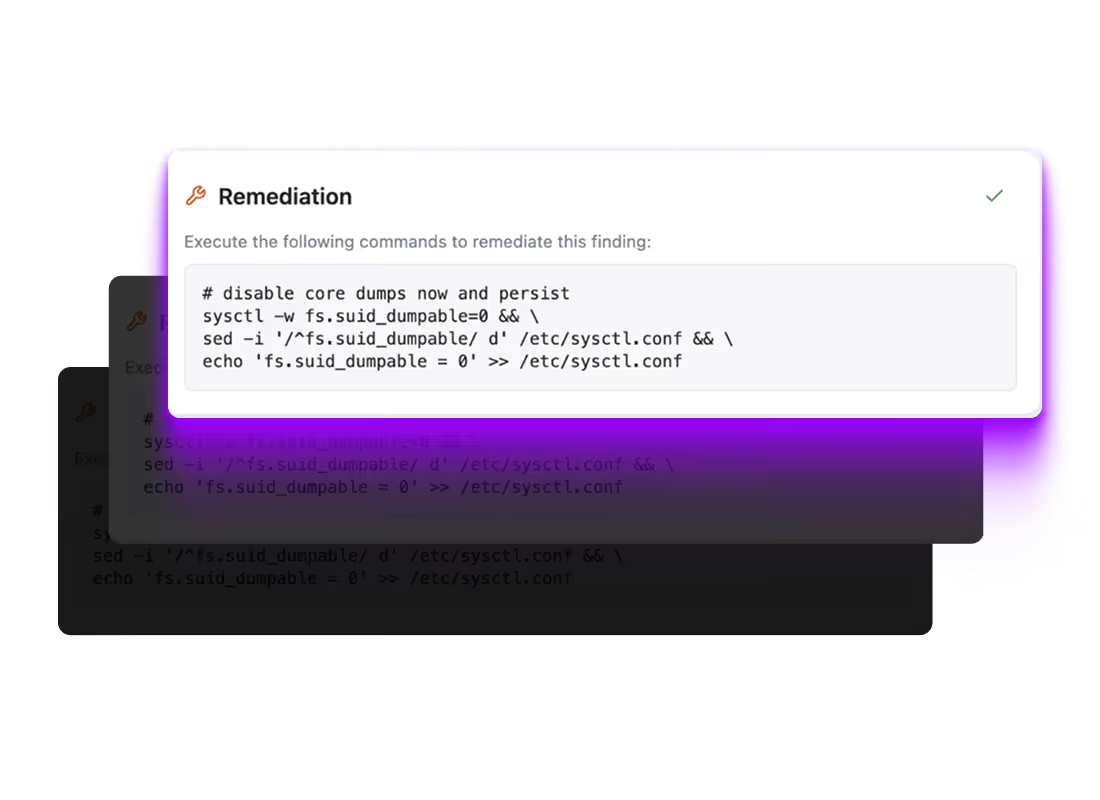
Embedded Secret & Config Risk Discovery
Beyond source code: Hardcoded credentials and insecure defaults are the primary targets for adversaries, yet they are often missed by tools that only scan source code repositories.
Live scanning: Insights goes beyond "pattern matching" in code by scanning the live filesystem for active secrets, passwordless accounts, and vulnerable file permissions.
Active remediation: We don't just find the weakness, Periphery provides engineers with the remediation actions needed to harden the system in seconds.
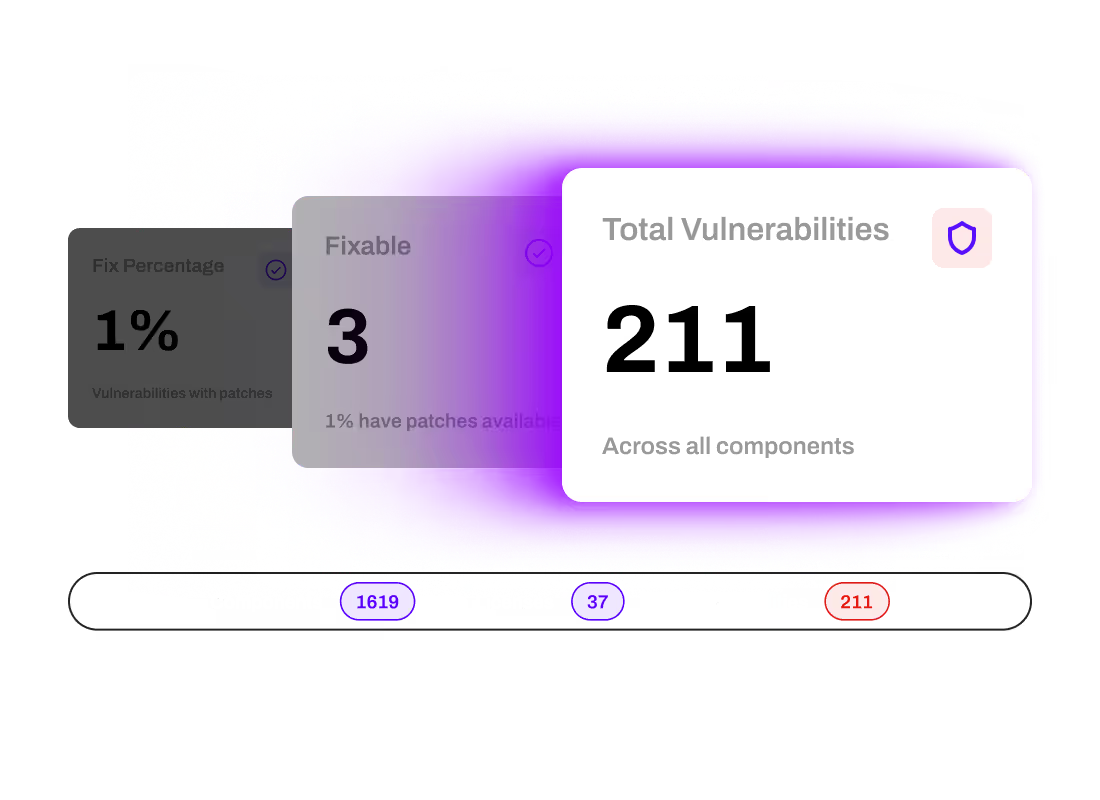
Reachability-Based SBOM Analysis
Tailored and targeted: Traditional scanners drown developers in thousands of "ghost" vulnerabilities found in dependencies that are never actually reachable or exploitable in your specific hardware configuration.
Unlike standard SCA tools that only check code imports, Insights combines deep SBOM data with live configuration evidence, such as enabled services and kernel modules, to filter out the noise.
Focused, efficient, secure: This allows your team to prioritize only the flaws that pose a documented, real-world threat to your product.
Compliance-as-Code for Global Regulations
Relieving the compliance burden: Mapping software to mandates like the EU Cyber Resilience Act (CRA), IEC 62443, or NIST 800-53 is a manual, weeks-long burden that traditional AppSec tools aren't built to solve.
Hours, not weeks: Insights automates this by mapping every finding directly to specific regulatory controls, generating audit-ready evidence and compliance scoring as a native byproduct of your build. This moves your product through internal and regulatory approvals in hours, not weeks.
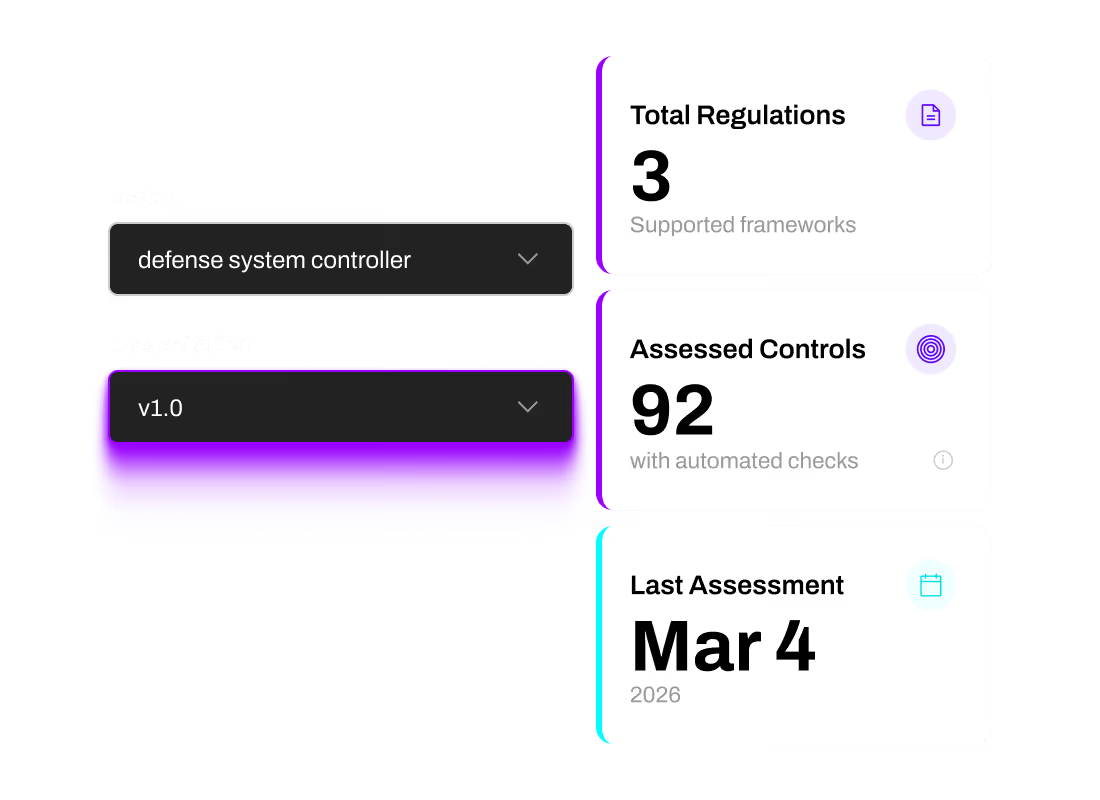

Insights looks to not only identify risks within the SBOM but also provide actionable recommendations, helping manufacturers address supply chain vulnerabilities before they become liabilities.
Insights simplifies this process by providing detailed evidence of device security and risk mitigation.
By demonstrating robust assessments, manufacturers can instill trust, strengthen relationships, and position their products as reliable and secure choices.




