Runtime Defense for Cyber-Physical Systems

Real-time defense for the high-stakes edge
Move beyond detection to autonomous system protection.
Periphery Outpost is a purpose-built runtime security agent for critical infrastructure and autonomous systems. It identifies and blocks sophisticated attacks in real-time, ensuring operational continuity for air-gapped critical infrastructure defense assets without the need for cloud connectivity.
Autonomous AI & Model Integrity
Defending Autonomy: For autonomous driving and robotics, the AI model is your most valuable IP and your biggest safety liability. Outpost monitors the runtime environment to prevent unauthorized access or manipulation of local AI tooling and proprietary model weights.
Safety-First Observability: In systems where uptime is non-negotiable, Outpost provides deep observability with a sub-3% CPU footprint. We ensure that security monitoring never interferes with real-time decision-making or critical system safety buffers.
IP Sovereignty: By operating entirely on-device, Outpost protects your proprietary algorithms from extraction. No sensitive model telemetry or training data ever leaves the local environment.
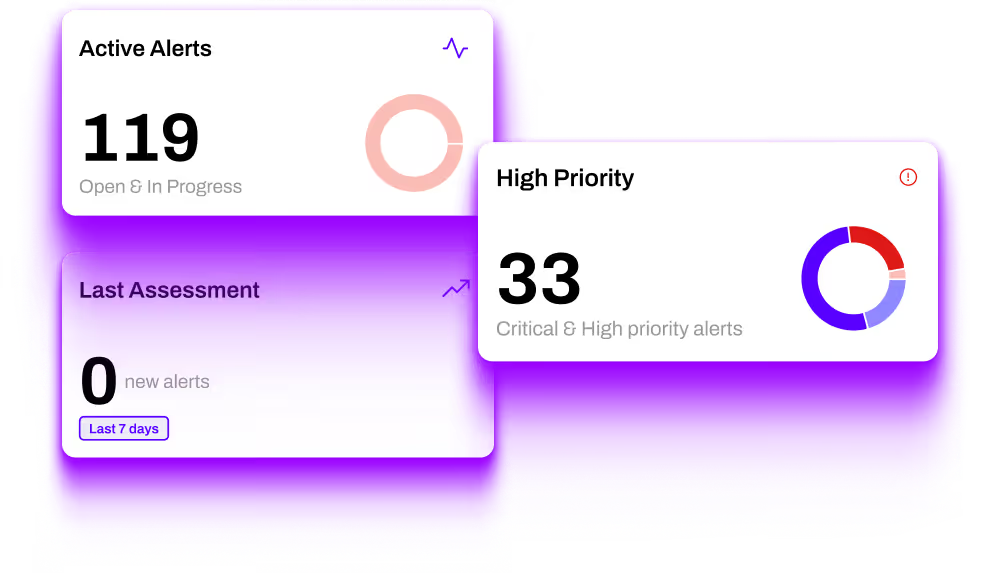
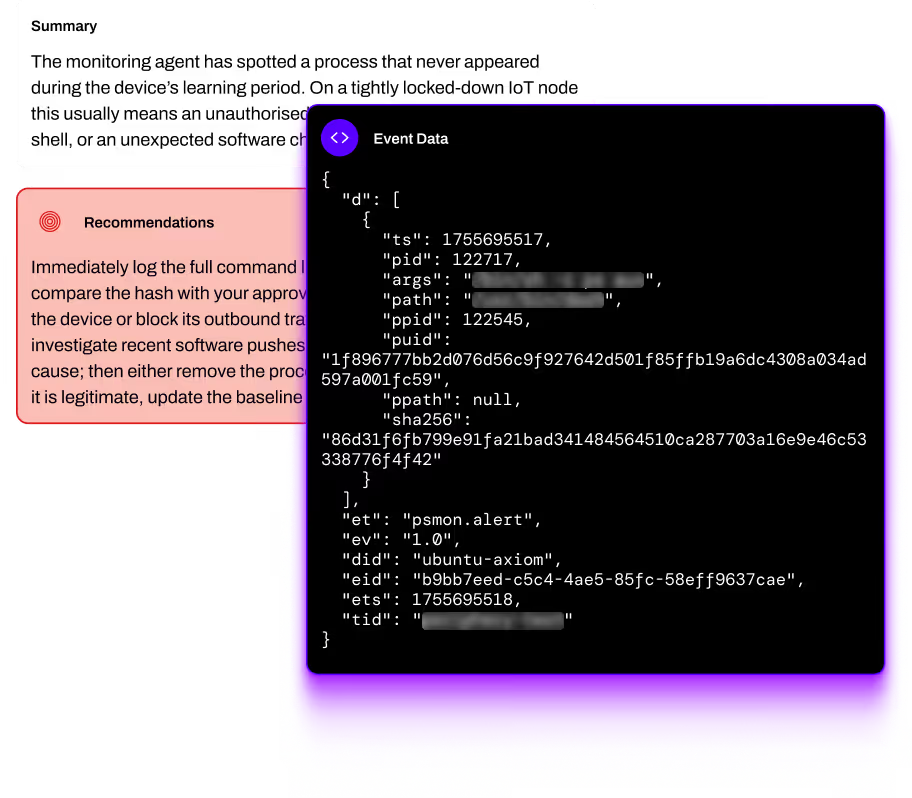
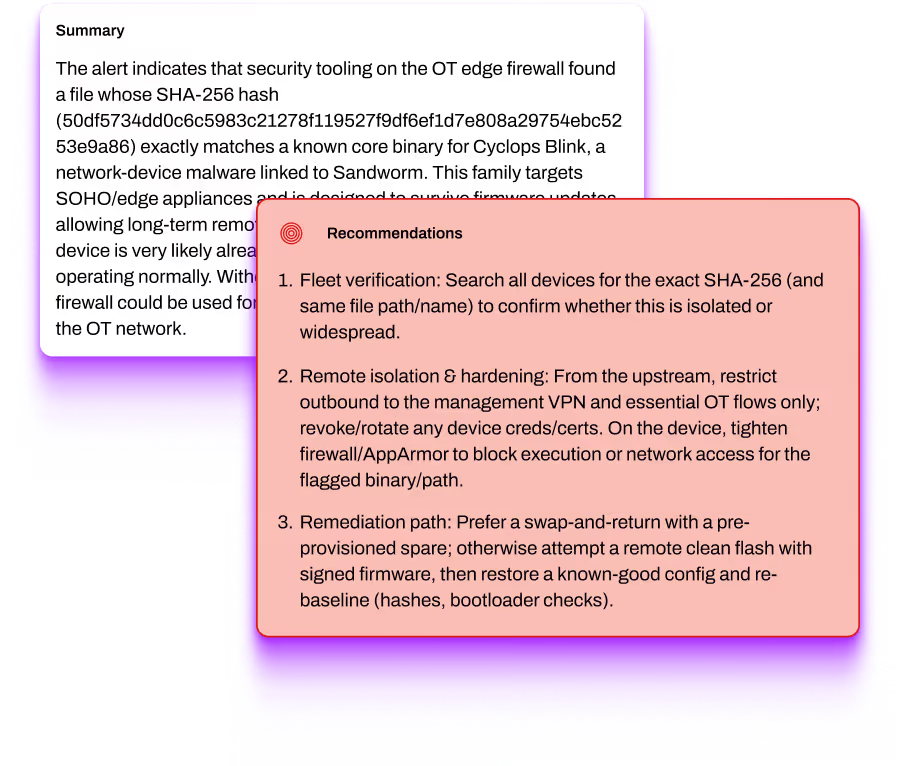
Behavioral Threat Detection
Modeling the mission: Traditional EDR depends on signature databases and cloud-heavy analysis - luxuries that autonomous drones and remote substations don't have.
Self-Contained Logic: Outpost uses on-device behavioral analysis to model "normal" system behavior at the kernel and application layers. This allows it to identify zero-day exploits and anomalous activity without a single signature update.
Deterministic Action: When drift or manipulation is detected, Outpost acts autonomously to block malicious processes and isolate threats locally. This maintains system integrity even when completely offline or in denied environments.
Continuous Attestation for CNI & Defense
Always-on compliance: Regulatory mandates like the EU CRA require manufacturers to monitor and report security incidents throughout a product's entire lifecycle.
Evidence Trail: Outpost provides the tamper-evident runtime logs and audit-ready receipts needed to prove your system is still hardened and compliant months after deployment.
Sovereign Data Control: Built for sensitive environments, Outpost operates entirely on-premise. Your assessment data remains in your control, preserving absolute system sovereignty in restricted or air-gapped zones.
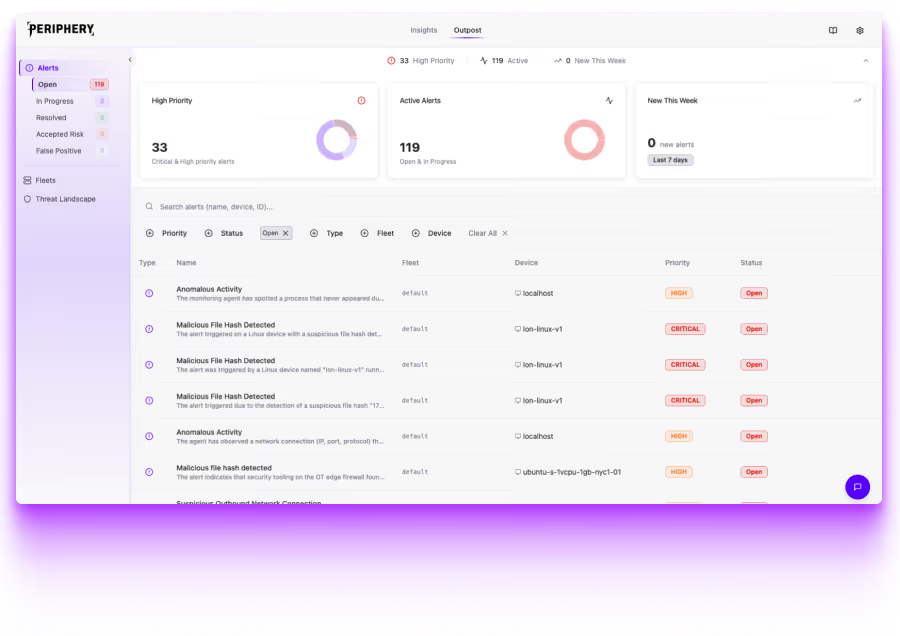
Outpost is Periphery’s real-time threat monitoring solution, purpose-built for embedded devices operating in dynamic environments. Unlike traditional EDR solutions designed for enterprise endpoints, Outpost is tailored for resource-constrained technologies, focusing on the device layer for Linux and the application layer for RTOS. It provides a continuous defense against the evolving threat landscape, helping organisations maintain operational integrity and security compliance.





